When you’re building trust with your customer base. And creating contracts that protect the data that they upload to your platform one thing you’ll need to address is the issue of personally identifiable data. For a tech startup you’ll be aware that customers upload a lot of data on to your platform. You spend time building trust with them so that they feel comfortable to do this. Contracts often highlight personally identifiable data as particularly noteworthy. Which begs the question of what exactly is personally identifiable data?
Some products require the upload of data that is clearly personally identifiable, for example a piece of payroll software. A user will have to upload their name, phone number, birthday, home address, social security number (or local tax ID number). All of which as undeniably identifiable. But what about your platform only asks a user to sign up with an email and a password, perhaps a name. Are these personally identifiable data? Let’s have a look.
The Critical Significance of PID Protection:
Within the tech startup landscape, safeguarding personally identifiable data (PID) emerges as a pivotal concern. As these startups engage in B2B transactions, the exchange of sensitive information, from customer data to proprietary software details, is inevitable. Protecting PID transcends being merely a legal requisite; it’s foundational for building and maintaining trust and credibility in the industry.
Deciphering Personally Identifiable Data (PID):
PID encompasses a broad spectrum of data, spanning names, addresses, email addresses, phone numbers, and specific identifiers like social security or financial information. For tech startups, PID extends to encompass data related to software usage, customer preferences, and other proprietary insights.
If you’re questioning whether email and name qualify as PID, then you need not wonder any further.
Yes, email addresses and names generally qualify as personally identifiable data (PID) from a privacy perspective. Personally identifiable information encompasses any data that can identify a specific individual. Both email addresses and names can uniquely identify individuals or, when combined with other data, contribute to their identification.
Here’s why email addresses and names are considered PID:
- Email Addresses: An email address is a unique identifier for an individual in the online world. It not only identifies the person but also serves as a means of communication and often as a login credential. For various online accounts. Because email addresses are unique to individuals. And can be used to contact or interact with them directly, they are considered personally identifiable information.
- Names: Names are one of the most basic pieces of personal information that can identify an individual. While names may not always be unique, they are still significant identifiers, especially when combined with other information like email addresses, physical addresses, or other demographic data. Names are commonly used in various contexts, including communication, transactions, and record-keeping, making them important pieces of personally identifiable information.
From a privacy standpoint, organizations are typically required to handle personally identifiable information with care and ensure that it is collected, processed, and stored securely, in compliance with relevant privacy laws and regulations such as the General Data Protection Regulation (GDPR) in Europe or the California Consumer Privacy Act (CCPA) in the United States.
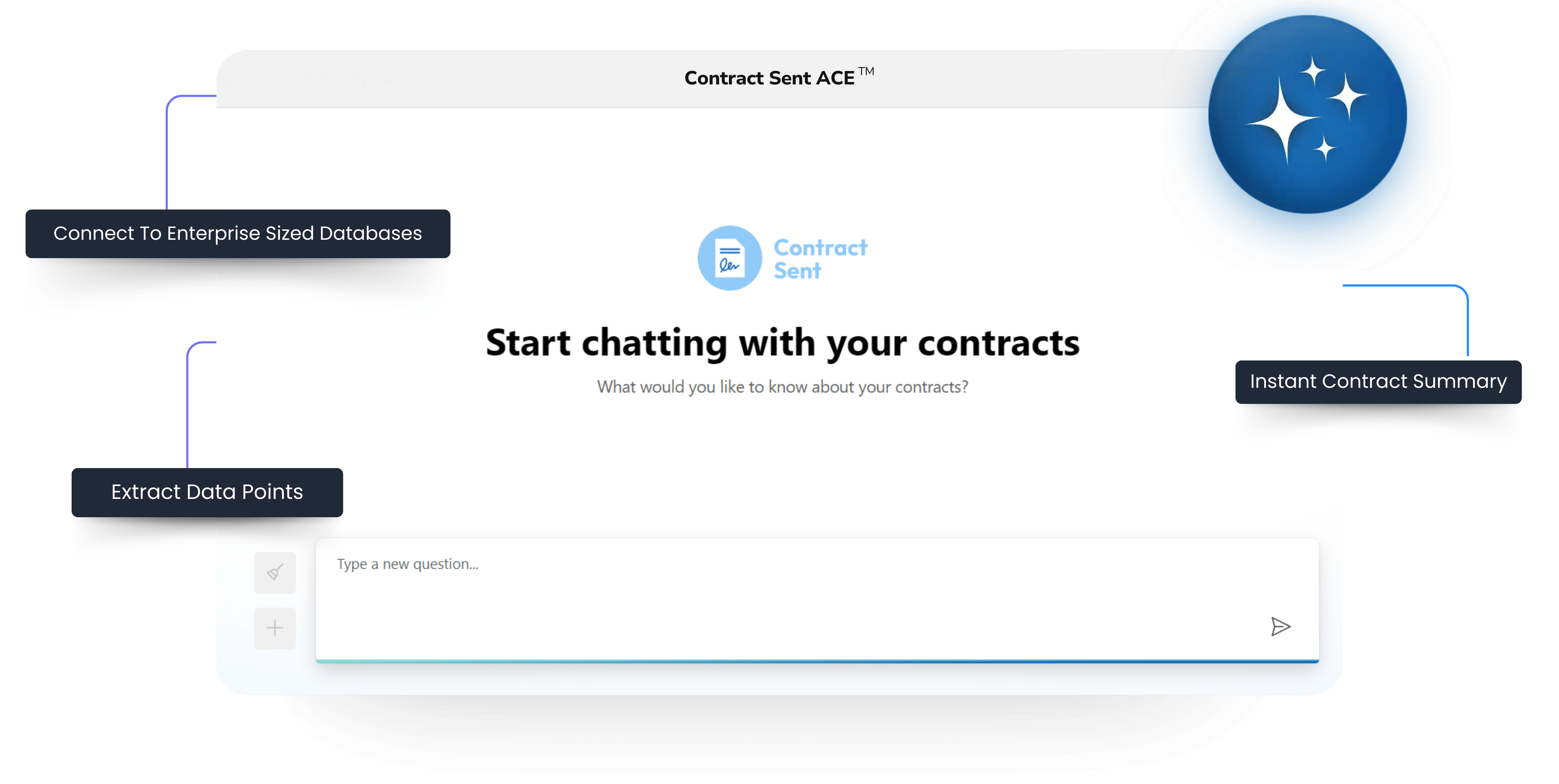
Redline What Matters
Raise Changes For Approval To Turnaround Contracts Faster
The Crucial Role of Legal In The Protection Of PID
Protecting customers’ personally identifiable data is crucial for startups to maintain trust, comply with legal requirements, and avoid potential penalties or reputational damage. Here are some key steps startups can take from a legal point of view to protect customers’ personally identifiable data:
Understand Applicable Laws and Regulations:
Startups should familiarize themselves with relevant data protection laws and regulations applicable to their operations, such as the General Data Protection Regulation (GDPR) in the European Union, the California Consumer Privacy Act (CCPA) in the United States, or other regional laws. Understanding these laws helps ensure compliance and informs the development of data protection practices.
Implement Privacy Policies and Notices:
Startups should create clear and comprehensive privacy policies that outline how they collect, use, disclose, and protect customers’ personally identifiable information. These policies should be easily accessible to customers and provide transparent information about data practices. Additionally, startups should provide privacy notices at the point of data collection to inform customers about specific data processing activities.
Obtain Consent for Data Processing:
Startups should obtain explicit consent from customers before collecting, processing, or sharing their personally identifiable data. Consent should be freely given, specific, informed, and unambiguous, and customers should have the option to withdraw consent at any time. Startups should also ensure that they have mechanisms in place to record and document consent.
Implement Data Minimization Practices:
Startups should adopt data minimization principles, collecting only the personally identifiable information that is necessary for the intended purpose and retaining it for the minimum amount of time required. By limiting data collection and retention, startups can reduce the risk of unauthorized access, misuse, or data breaches.
Secure Data Storage and Transmission:
Startups should implement appropriate technical and organizational measures to secure customers’ personally identifiable data against unauthorized access, disclosure, alteration, or destruction. This includes encryption, access controls, regular security audits, and training employees on data security best practices. Additionally, startups should ensure secure transmission of data over networks, such as using encryption protocols for online transactions.
Provide Data Subject Rights:
Startups should respect customers’ data subject rights, including the right to access, rectify, delete, or restrict the processing of their personally identifiable data. Startups should establish procedures for handling data subject requests and respond to such requests in a timely and transparent manner.
Vendor Management and Due Diligence:
Startups should carefully vet and monitor third-party vendors or service providers that have access to customers’ personally identifiable data. This includes conducting due diligence on vendors’ data protection practices, ensuring they have appropriate security measures in place, and including contractual provisions that address data protection responsibilities and liabilities.
Incident Response and Breach Notification:
Startups should develop and implement an incident response plan to effectively respond to data breaches or security incidents involving customers’ personally identifiable data. This includes promptly investigating incidents, mitigating risks, and notifying affected individuals and relevant authorities in accordance with legal requirements.
Provide Employee Training and Awareness:
Startups should invest in employee training and awareness programs to educate staff about their responsibilities regarding data protection and privacy. Employees should understand the importance of safeguarding customers’ personally identifiable data, recognize potential risks, and know how to handle data securely and compliantly.
Regular Compliance Audits and Reviews:
Startups should conduct regular compliance audits and reviews of their data protection practices to ensure ongoing adherence to applicable laws and regulations. This includes reviewing and updating privacy policies, conducting risk assessments, and addressing any gaps or vulnerabilities identified through audits.
By proactively implementing these legal measures to protect customers’ personally identifiable data, startups can build trust with their customers, demonstrate commitment to data privacy, and mitigate legal and repetitional risks associated with data breaches or non-compliance.
As tech startups navigate the complexities of data protection, safeguarding personally identifiable data is non-negotiable. Addressing this in your contract negotiation process will help to create trust with your customer. Ultimately if you want to close B2B deals fast, this trust building can be one of best ways to speed up this process.